If you think technology can solve your security problems, then you don’t understand the problems. And you don’t understand the technology. – Bruce Schneier
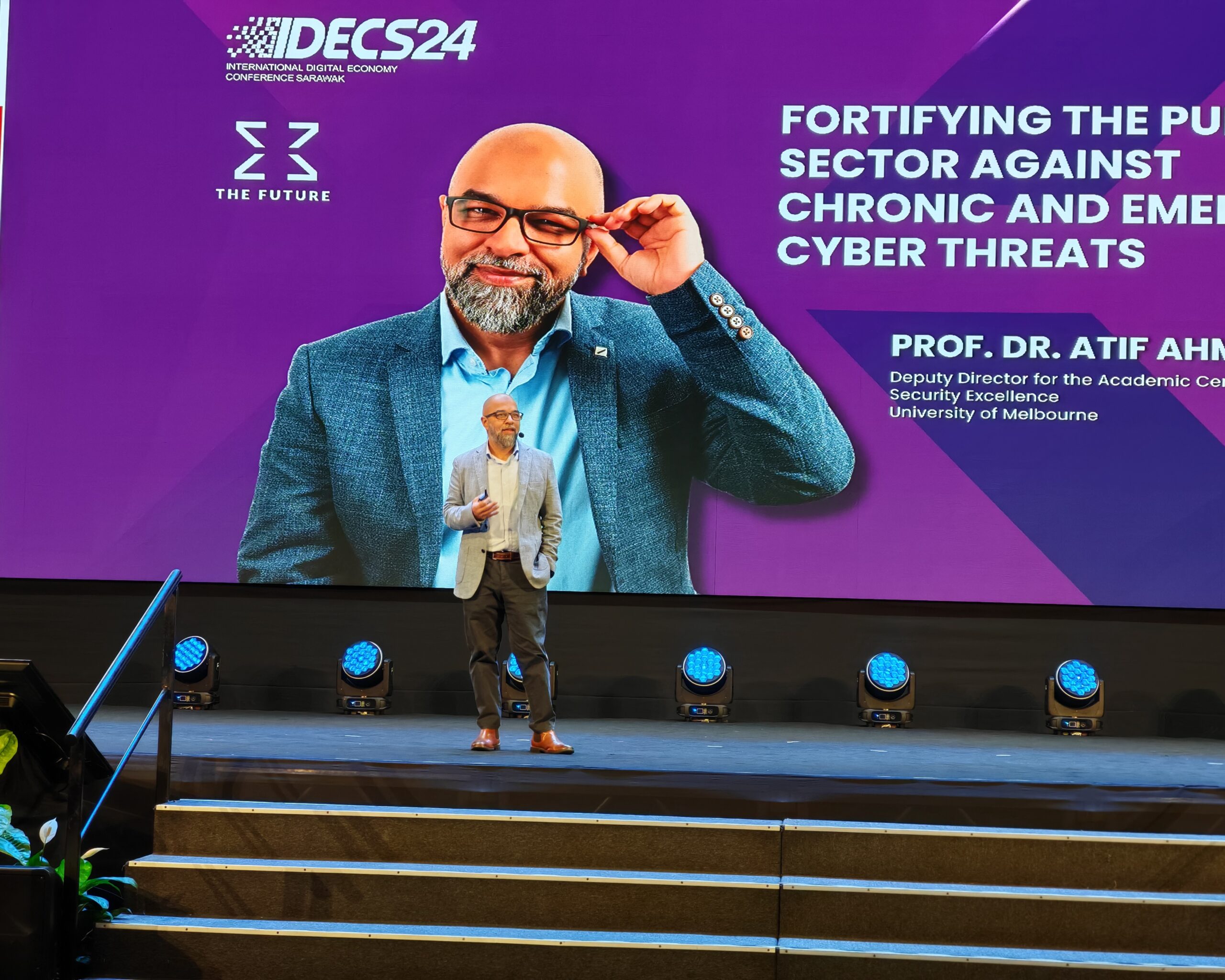
Prevention is always better than cure. In this context, the University of Melbourne’s Deputy Director for the Academic Centre of Cyber Security Excellence, Professor Dr Atif Ahmad, shared strategies to fortify against chronic and emerging cyber threats at the recent IDECS.
Cyber Resilience
The convenience of the transition towards digitalisation is apparent. However, vulnerabilities can arise within organisations, especially when their cyber defences are not up to par.
Understanding cyber threats and the challenges of strengthening cyber defences within public sectors, the University of Melbourne’s Deputy Director for the Academic Centre of Cyber Security Excellence, Professor Dr Atif Ahmad, shared strategies to fortify against chronic and emerging cyber threats at the recent International Digital Economy Conference Sarawak (IDECS).
With almost three decades in the industry, Dr Atif is currently leading two research teams to help Malaysia build its cyber defence capabilities. He is also working with the National Cyber Security Agency (NACSA) to develop new tools and resources to strengthen defences against the inevitable cyber attacks that may come.

In further elaboration, he explained that cybersecurity is a problem that does not solely stem from technology.
“It is a business problem with some technology solutions, but many of the solutions are people solutions and process solutions. To solve the problem, you need to consider people versus technology and fuse them together.”
What threat actors should we be concerned about regarding cyber attacks?
⦁ Script kiddies: An unskilled individual who uses scripts or programmes developed by others primarily for malicious purposes.
⦁ Sophisticated hackers: Often exploit human vulnerabilities through social engineering tactics, which can include targeted phishing emails where they impersonate trusted entities to trick individuals into divulging sensitive information.
⦁ Insiders: That disgruntled employee sabotaging from within.
⦁ Organised and sophisticated threat actors: The ones that spent six months to a year studying a firm in the background, then figured out their strengths and weaknesses, and had a thorough plan to attack.

The impact of cyber attack
When an attack occurs, there are two different types of impacts, said Dr Atif. One is above the surface — better known as the costs associated with a cyber incident, such as public relations, cybersecurity improvements, regulatory compliance, technical investigations, and others.
However, the impacts below the surface are the ones that prolong complications, including increased costs to raise debt, the effects of operational disruption or destruction, the value of lost contract revenue, devaluation of the trade name, and others.
“Most people think about the next few days after a cyber attack, which involves realising they’ve been compromised, restoring their services, and patching the vulnerability. But that’s just the first stage,” he said.

“The next phase involves lawyers, media, and public relations. Your focus then shifts to redesigning the organisation to prevent a recurrence. This constant shifting of focus can have a significant impact on the company.”
Fortifying cyber defence in public sector
The public sector, which includes national data, healthcare, banks, and more, is an essential digital infrastructure for a country. Therefore, cybersecurity in the public sector is vital, as it not only protects data but also helps maintain public trust and ensure the continuity of essential services by safeguarding this infrastructure.
However, challenges may arise in the public sector when it comes to fortifying cyber defences or addressing a cyber attack. Among the challenges Dr Atif shares are:
⦁ Bureaucratic norms in practice
⦁ Resourcing constraints
⦁ Complex asset base
⦁ Legacy systems
⦁ Talent shortage
But the most crucial challenge to note is the culture of an organisation. According to the professor, “culture eats strategy for breakfast”, meaning that no matter how comprehensive the plan is to change an organisation’s cybersecurity, strategy, or practices, it will not work if it doesn’t align with the way people think or behave.
“So the elephant in the room is culture. Any strategies you try to implement that go against your company’s culture are bound to fail,” he added.
When fortifying the public sector, Dr Atif said that it is important to address the culture first. Issues such as bureaucracy, a lack of urgency, and the inability to attract good talent are among those that need to change.

“You need to change the culture from compliance-driven approaches to defence-driven approaches. Just because you’re compliant does not mean you’re secure. What we have to build first is this defensive mindset, and the second thing is that we need to learn to measure our capabilities.”
In an insightful talk during the day, Dr Atif concluded his sharing by saying that a threat actor cannot be dealt with simply.
“As a company, you need to treat a malicious attack like a chess game. We need to train our cyber leaders to play chess in cyber. And that’s another skill that public servants will need to be trained in.”